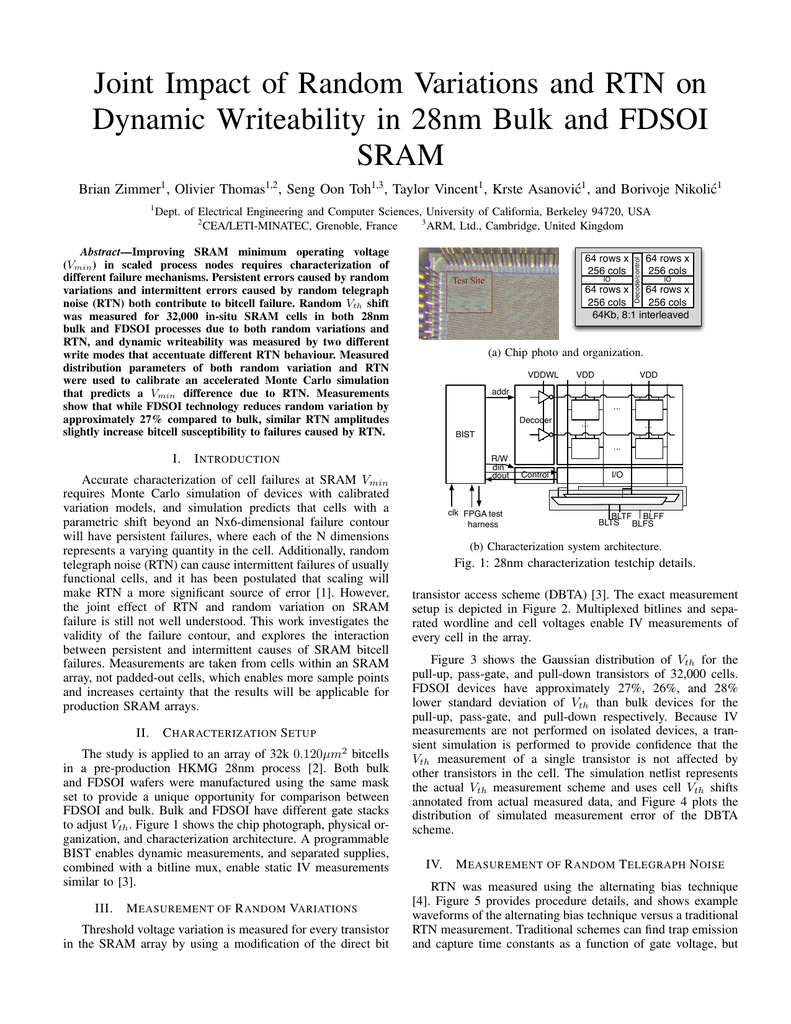
The Impact Of Joiner s First Component Video
\The Impact Of Joiner s First Component - apologise
A breach is, generally, an impermissible use or disclosure under the Privacy Rule that compromises the security or privacy of the protected health information. An impermissible use or disclosure of protected health information is presumed to be a breach unless the covered entity or business associate, as applicable, demonstrates that there is a low probability that the protected health information has been compromised based on a risk assessment of at least the following factors:. Covered entities and business associates, where applicable, have discretion to provide the required breach notifications following an impermissible use or disclosure without performing a risk assessment to determine the probability that the protected health information has been compromised. The second exception applies to the inadvertent disclosure of protected health information by a person authorized to access protected health information at a covered entity or business associate to another person authorized to access protected health information at the covered entity or business associate, or organized health care arrangement in which the covered entity participates. In both cases, the information cannot be further used or disclosed in a manner not permitted by the Privacy Rule. The final exception applies if the covered entity or business associate has a good faith belief that the unauthorized person to whom the impermissible disclosure was made, would not have been able to retain the information. Covered entities and business associates must only provide the required notifications if the breach involved unsecured protected health information. Unsecured protected health information is protected health information that has not been rendered unusable, unreadable, or indecipherable to unauthorized persons through the use of a technology or methodology specified by the Secretary in guidance.![[BKEYWORD-0-3] The Impact Of Joiner s First Component](https://www.researchgate.net/profile/Llorenc_Cabrera-Bosquet/publication/221964780/figure/fig1/AS:281763227160579@1444188996257/Biplot-of-the-first-and-second-principal-component-axes-of-the-effects-of-1-148-SNPs-on-3_Q320.jpg) The Impact Of Joiner s First Component
The Impact Of Joiner s First Component
Definition of Breach
Mar 03, Sharmila Arasu 5 min. Mar 03, Ignacio Pozuelo 2 min.
NetworksNetwork slicingNetwork Services. Mar 01, Marcelo Malizia 4 min. Mar 01, Caroline Berns 1 min. People and careers. Feb 26, Justin Paul 3 min. Feb 25, Torsten DuddaAlexey Shapin 5 min.
Information Menu
Feb 24, Treasa Dovander 3 min. Feb 23, Jasmeet Sethi 4 min. Feb 23, Taimur Lodhi 3 min. Digital transformationIndustry 4.
Junior Achievement USA is a nonprofit that inspires and prepares young people for success
Feb 19, Caroline Berns 1 min. Edge computingResearch. The Ericsson Blog We make complex ideas on technology, innovation and business simple.

Subscribe now. Home Ericsson Blog. Expert tips for future leaders in cloud native 5G Core. Enablers for 5G success: learnings from North America.
Feb 25, Torsten Dudda Alexey Shapin 5 min. A technical overview of time-critical communication with 5G NR.]
Willingly I accept. The theme is interesting, I will take part in discussion. I know, that together we can come to a right answer.
Big to you thanks for the help in this question. I did not know it.
Quickly you have answered...
Very interesting phrase
I to you will remember it! I will pay off with you!